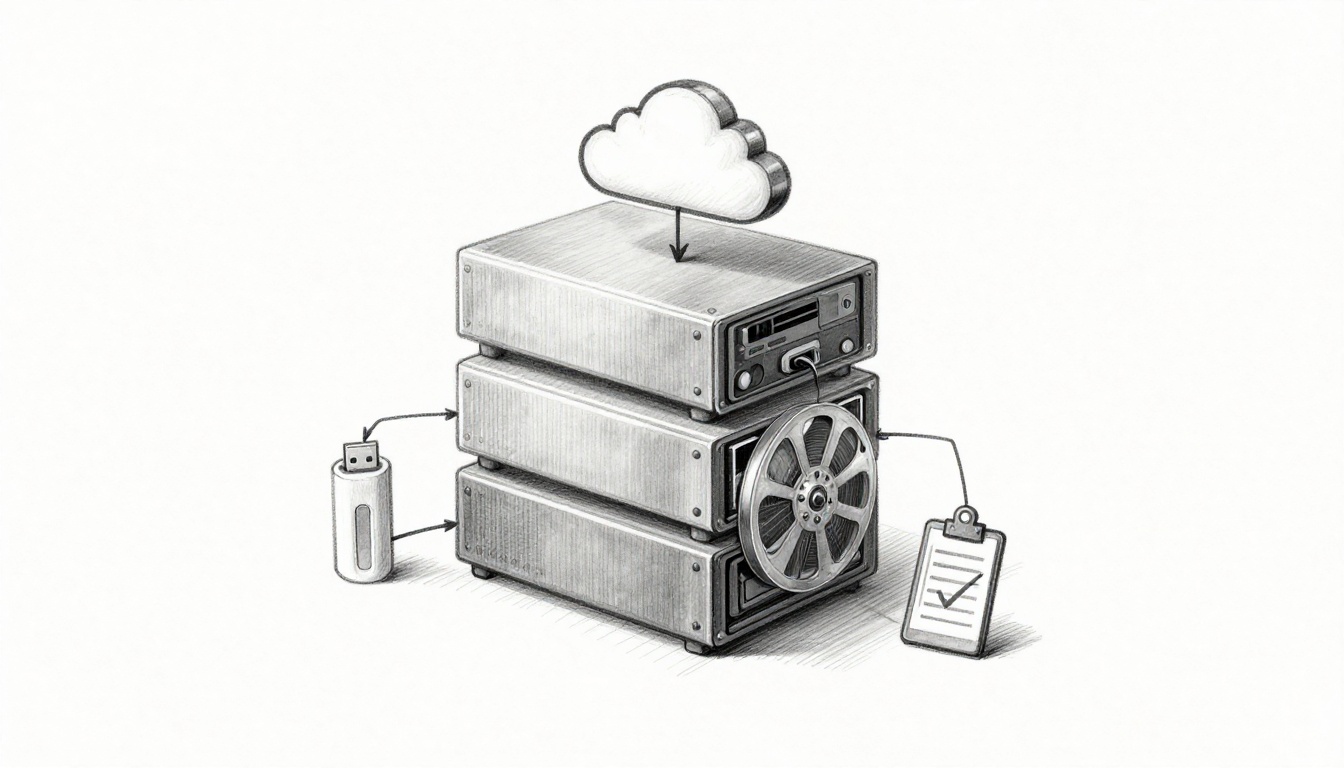
How to Create a Verified 3-2-1 Backup Strategy for Your Data (3-2-1-1-0 in 2026)
You can have backups, and still lose data. That’s what makes ransomware so cruel, it doesn’t just steal files. It tries to destroy or encrypt your recovery points too. In the first months of 2026, ransomware kept hitting U.S. organizations at a high pace. For example, Bitdefender’s analysis of early 2026 reporting shows a steady … Read more